Using wget Linux command
By rolando
/ December 8, 2021
wget is a command-line, open-source utility to download files and web pages from the internet. It gets data from the...
Read More
Tags: wget
The “New Normal”
By rolando
/ December 5, 2021
2020 The year of the "New Normal" Without a doubt, this year 2020 has been a year of radical changes....
Read More
MacOS X – Big Sur – SMB/Windows shared folder Issues connecting
By rolando
/ July 8, 2021
This kind of incident occurs for two reasons, 1 - It is possible that the Login information stored in the...
Read More
rsync command
By rolando
/ August 22, 2020
The rsync or remote sync, is a Linux/Unix command utility used to synchronize and copy files and directories either locally...
Read More
Hackers Using Google Analytics to Bypass Web Security and Steal Credit Cards
By rolando
/ June 23, 2020
by: Ravie Lakshmanan from The Hacker News Researchers reported on Monday that hackers are now exploiting Google's Analytics service to...
Read More
Tags: cybersecurity
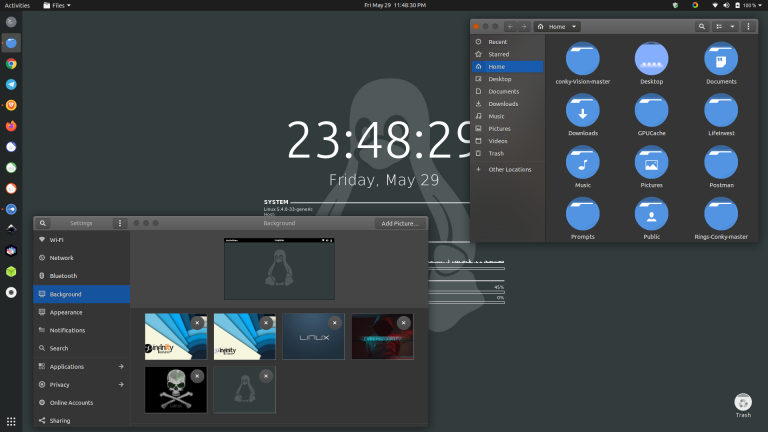
Ubuntu Desktop Makeover
By rolando
/ May 30, 2020
I must confess that since Ubuntu started, there have been a lot of changes that we have experienced on our...
Read More